Revealed: Hackers can turn Google, Siri against you
10/28/2015 / By usafeaturesmedia
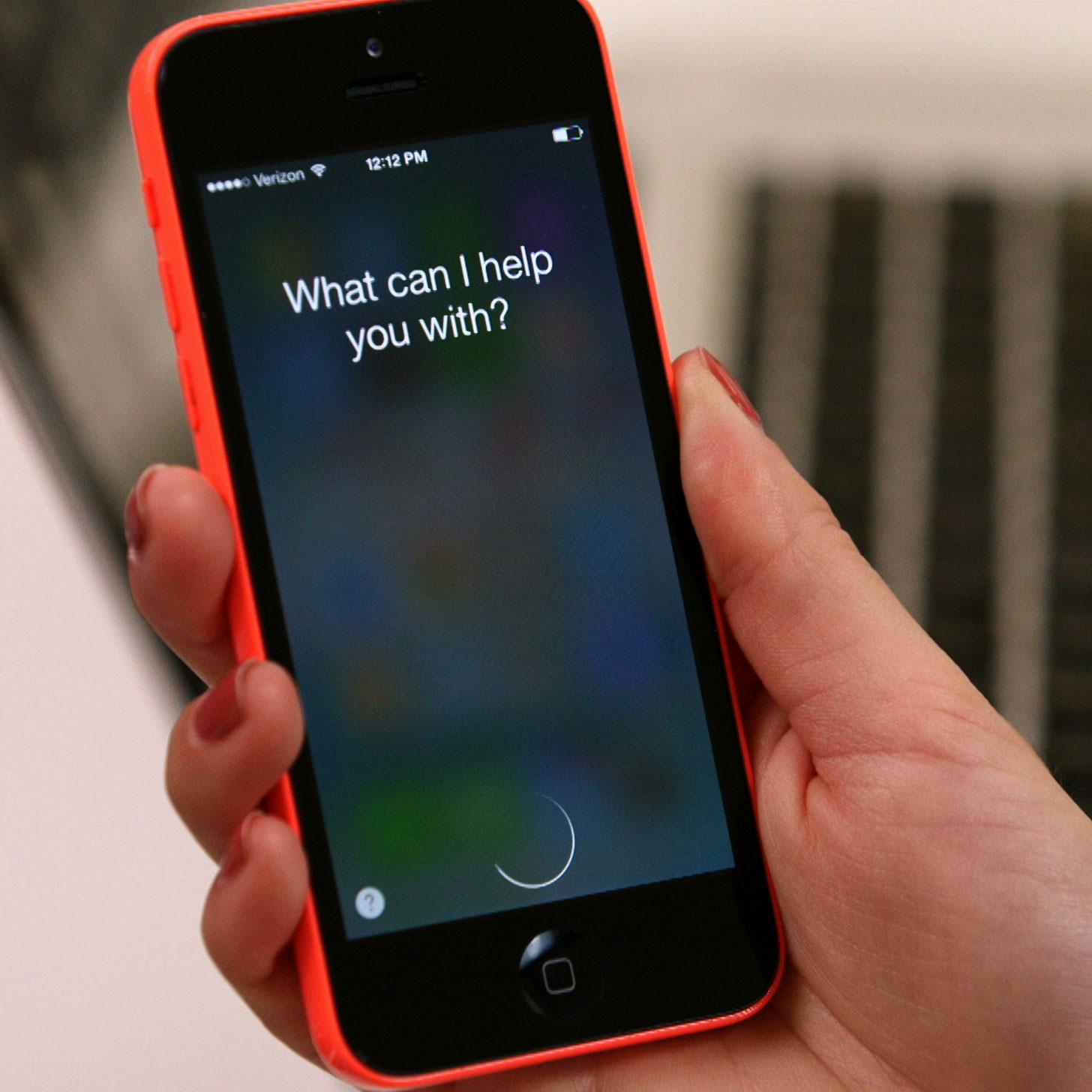
(Cyberwar.news) A new feature for iOS 9 is the ability to train the iPhone’s “Siri” search function to only recognize your voice so your phone does not respond to commands from just anyone, but according to a new cybersecurity report, researchers have found a way to use radio waves to silently activate Siri or Android’s Google Now from across a room, InHomelandSecurity.com reports.
Cyber security researchers from ANSSI, an agency of the French government, say the hack only works if the target device has Siri or Google Now enabled, and has headphones or ear buds plugged in that also contain a microphone.
Further reporting from WIRED notes:
“Their clever hack uses those headphones’ cord as an antenna, exploiting its wire to convert surreptitious electromagnetic waves into electrical signals that appear to the phone’s operating system to be audio coming from the user’s microphone.”
Theoretically, the hack could be used to activate any function involving Siri or Google Now voice interaction. Researchers said that hackers could make calls, send texts, open malicious code on key websites, send phishing attacks or spam, or post to social networks like Facebook and Twitter. In addition, placing an outgoing call to the hacker’s own phone would enable the hacker to eavesdrop unnoticed on the victim.
- Have you ‘liked’ Cyberwar.news on Facebook? Click here!
“That’s the doomsday scenario version. Now, let’s scale it back and look at how plausible it is for an attack like this to actually work,” InHomelandSecurity.com reported. “Most of the time that you have headphones plugged in to your smartphone you’re also listening to them. When Siri or Google Now are activated—even if initiated silently over the airwaves—they typically make some sort of noise indicating that they’re ready to listen to your voice command, and they respond verbally by default so if you’re wearing the headphones you should immediately realize something suspicious is going on.”
Even if you are not currently actively using headphones – perhaps they are plugged in but your phone and headphones are just sitting on the table in front of you – it would be difficult to activate the virtual assistant without your knowing it.
Generally, the display comes on when the function is activated, along with a response from Siri or Google Now. If you’re just sitting there enjoying the day and your phone starts talking to you, you’d probably notice that.
Still, it’s a security concern, experts note.
“Additional functionality, especially concerning user convenience, has often come at the cost of some security,” stressed Gavin Reid, VP of threat intelligence for Lancope. “In this case the hack needs proximity to work and is a proof of concept needing specialized hardware. High security government equipment and installations have often come with additional shielding specifically to limit emanations and any covert channels.”
- ‘Who Knew 1’s and 0’s Could be so Dangerous?’ See the full merchandise collection at the Cyberwar.news Cyber Cafe now!
See also:
Tagged Under: Android, Google Now, hackers, iPhone, Siri, smart phones